Our Quantum Advantage challenge with $20,000 BTC award is live.
More Details →
Quantum cryptography is changing the way we think about data security. Unlike traditional methods that rely on complex mathematical algorithms, this advanced technique uses the principles of quantum physics to protect information in transit. It leverages the behavior of particles like photons to detect any attempt to intercept or alter data. With cyber threats, and especially quantum computing itself, posing a growing risk to current encryption systems, quantum cryptography offers a future-proof solution.

Quantum computing cryptography work is essentially a sophisticated method of encryption that uses the inherent properties of quantum mechanics—the quantum computing basics—to secure and transmit data in a way that is virtually invulnerable to hacking attempts.
While conventional cryptography relies on mathematical complexities for data protection, quantum cryptography introduces a new way to safeguard data, based on properties of quantum physics. This guarantees that any unauthorized access or interference would immediately alert the sender and receiver, making the system highly secure against potential threats.
The process depends on light particles, or photons, to transfer data through fiber optic cables, representing binary bits. These photons are key to the impermeability of quantum cryptography. This is due to three distinct quantum properties:
These traits make it impossible to measure or interact with the system's quantum state without causing a detectable disturbance. Photons, given their well-understood behavior and their critical role as information carriers in optical fiber cables, are the perfect candidates for this task.

Quantum cryptography includes a variety of protocols. Each of them works in different ways to protect information.
Quantum Key Distribution allows two parties to securely generate a shared encryption key using the principles of quantum mechanics. Unlike classical methods, QKD is based on the no-cloning theorem, which states that unknown quantum states cannot be copied without disturbing them. The most famous example is the BB84 protocol, where information is encoded in photon polarization states. Any attempt at eavesdropping introduces detectable anomalies, allowing the communicating parties to know if security is compromised. Once verified, the key can be used for classical encryption.
Quantum coin flipping is a cryptographic protocol that allows two distant parties to generate a random outcome, like flipping a coin, without trusting each other. In classical settings, one side can often cheat to bias the result, but quantum mechanics can prevent this. Using quantum states, each participant sends information in a way that prevents unilateral control. While perfect fairness is impossible, quantum coin flipping guarantees that the probability of cheating is limited by quantum uncertainty.
The Kek protocol is a lesser-known quantum cryptographic scheme designed for key exchange and secure communication. It uses entangled quantum states to make sure that cryptographic keys can be distributed with built-in eavesdropping detection. If someone tries to intercept or measure the entangled particles, the correlations between them collapse. This reveals the tampering attempt. The Kek protocol focuses on efficiency and resilience, aiming to extend QKD concepts with added strength for noisy environments.
The Y-00 protocol, also known as the Yuen protocol, is a quantum stream cipher that combines classical encryption with quantum noise to improve security. It encodes messages using coherent states of light and deliberately introduces quantum noise, making it extremely difficult for an eavesdropper to distinguish the correct key. Unlike QKD, Y-00 does not focus on generating a key from scratch but rather on encrypting classical data streams securely. It’s also compatible with existing optical communication infrastructure.
Position-based quantum cryptography authenticates a user based on their geographical location rather than a secret key or password. It relies on the fact that quantum information cannot be copied and transmitted faster than light. A verifier sends quantum challenges, and the prover must respond within a specific time frame from their claimed position. If the response comes from anywhere else, the timing and quantum state correlations will fail. This approach is potentially ideal for location authentication in applications like secure access, military defense, and satellite communications.
Device-independent quantum cryptography aims to guarantee security even if the devices used are untrusted or compromised. Instead of relying on the internal functioning of hardware, it bases security proofs on the violation of Bell inequalities, which demonstrate genuine quantum entanglement. This prevents cybercriminals from exploiting backdoors or imperfections in the system. The approach ensures secrecy based solely on fundamental quantum principles instead of device reliability.
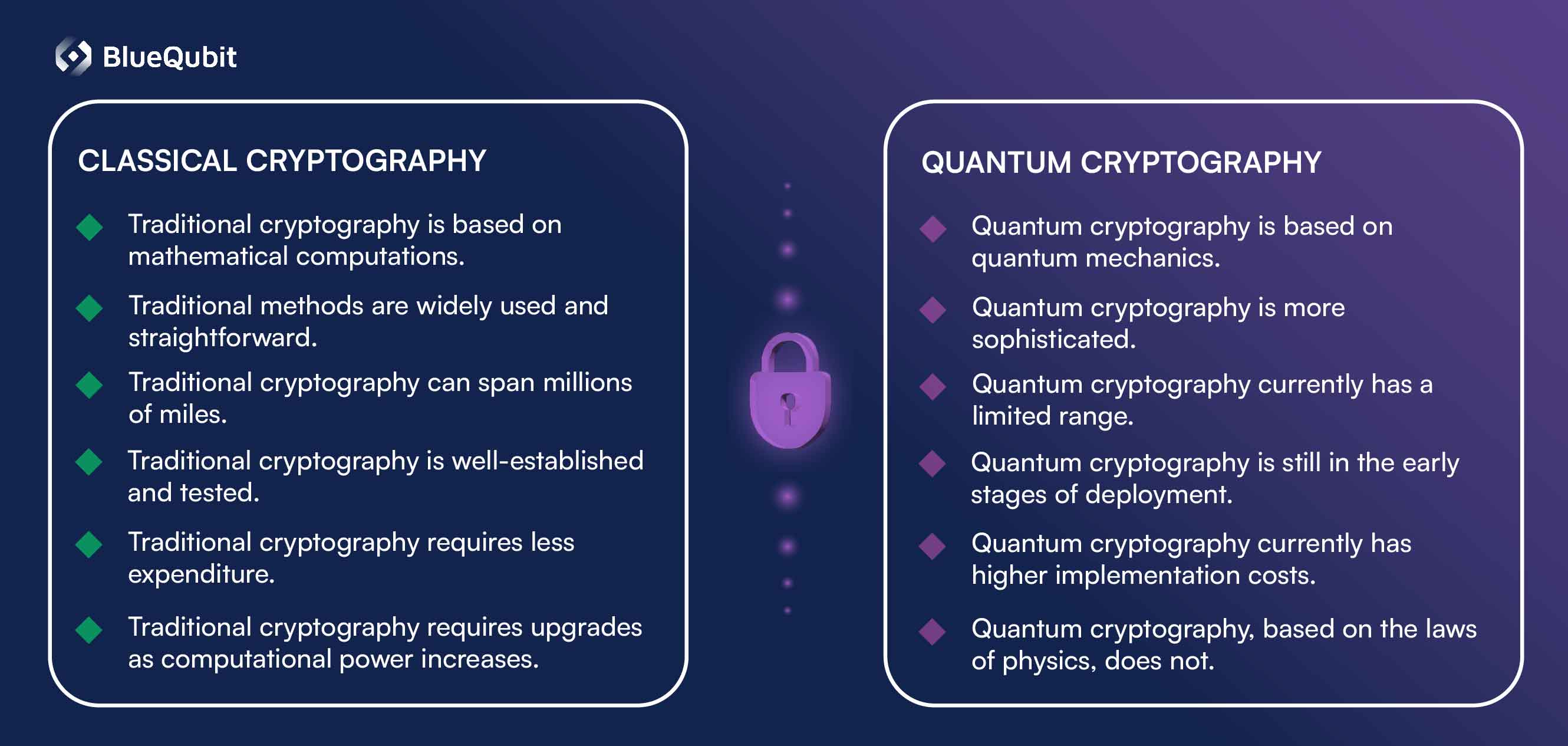
The concept of encryption is not new, but the ways we achieve it are continually evolving. While traditional cryptography has served as the foundation of secure communication for decades, the advent of quantum computing and cryptography is changing how we think about data security.
Traditional cryptography, including RSA and ECC algorithms, relies on mathematical computations that make it computationally challenging for unauthorized entities to derive private keys from public ones. However, as quantum computing advances, these traditional cryptographic techniques may no longer be sufficient, as the computational assumptions underlying their security eventually become compromised.
That’s where quantum cryptography comes in, using the quantum mechanical model for encryption. It's less about computations and more about the properties of quantum states. Its primary component, QKD, guarantees secure communication by making any attempt at eavesdropping detectable.
Despite its potential, however, quantum cryptography comes with its own set of challenges. To begin with, it's currently more expensive and more challenging to implement than traditional methods. Also, the range of quantum communication is limited, making it less suitable for long-distance communication.
Regardless of the challenges and the fact that it’s still in its early stages, quantum cryptography is already opening up new dimensions of data security that promise to surpass traditional cryptographic methods.
As one of the quantum computing use cases itself, quantum cryptography has emerged as a promising response to the growing threats posed by quantum technology to traditional cryptographic systems. However, like any technology, quantum cryptography also comes with its challenges. Understanding the advantages and limitations of this technology can help decision-makers plan a more secure, quantum-safe future.
]\p=
For professionals and researchers eager to experiment with quantum cryptography or develop cutting-edge quantum cryptographic algorithms, BlueQubit offers a user-friendly solution. Built on real quantum computing hardware and high-fidelity simulators, the platform serves as an environment where you can:
With intuitive API access, comprehensive documentation, and a supportive community, BlueQubit allows researchers, developers, and cryptographers to push the boundaries of secure communication and prepare for a quantum-secure future.
As applied quantum computing continues to advance, the future of cryptography is taking form in real time. Traditional encryption methods are no longer enough, prompting researchers and businesses to explore quantum solutions. Technologies like QKD are paving the way for a more secure digital landscape. Meanwhile, companies like BlueQubit are making it easier to experiment, innovate, and stay ahead of emerging threats. While challenges remain, the integration of quantum principles into cryptographic systems signals a major shift—one that will redefine cybersecurity down the line.